The human race has always worked to make their job easier. Carrying heavyweights was difficulty so the wheel was invented. The first tool/machine made to make the task easier. Carrying food, tools, wood and other survival equipment became easier. This tool made life easier. The man had overcome an obstacle and created ease for the entire human race.
We the human race or Homo sapiens are known to be social animals. Interaction and emotions are what distinguishes us from the rest of the beings. This need to interact called for the invention of phones. This technology has taken turns for the better and we have much more sophisticated means of telecommunication.
At the very center of today’s communication systems is the internet. The light that shines in every house. The one thing that keeps us connected, educated and entertained. From websites to apps, everything for the human race. A small book that has everything in it, an entire virtual world.
The Fountain of Opportunity
The internet was opened for public use around 1994. A limited number of people had access to it. By December 1995, there were only 16 million people using the internet. As the technology improved and became cheaper, users grew. Infrastructure development had a big hand in this expansion too.
By September 2002, 9.4% of the global population was using the internet. Roughly 7 years on and the internet users around the globe had jumped to a staggering 587 million. Now that’s progress. This opened new avenues, new channels, and opportunities. Everyone by this time knew about the internet and wanted a piece of it.
Introduction of social networking websites really brought the world to it. Those who were hesitant came forward to be a part of it. Soon the internet was a need. A need, a necessity with which life was difficult. Fast forward a few years and mobile internet came to the fold. This was a leap forward. Internet in your palm. A world of information and entertainment in your palms. Pay bills, shop and so much more with a single click.
By December 2017, 54.4% of the world population was using the internet. Meaning? The Internet is accessible for more than half of the world population. Internet no longer is a communication line but a market that is filled business. Everyone has their virtual stores, online markets, and presence on the internet. Universities use their websites for announcements. Big brands offer special discounts to their clients that prefer shopping online. The internet revolution is real!
The Downside
This tremendous opportunity created so many options. Shopping, recreation, health, education and so many more. We can now sit back home and get everything on our doorstep. Life is easier and everything so much more convenient. Never leave the house and miss out on nothing. The entire world where we are.
So much power and opportunity not always gets the right kind of attention. These opportunities are unlimited and have no boundaries. Like everything else, this opened doors to those with sinister motives. There were those who would sneak and take what they want. Yes, hackers!
A simple term that defines an attack, hostile takeover a theft, hacking. With so much information and money to loot, the attacks grew. With time strong and much more sophisticated. This caused many complications for those trying to come out on the top.
According to the Congressional Small Business committee, 71% of cyber-attacks happened at businesses. These businesses usually have less than 500 employees. So small and medium-sized business are at the receiving end of these attacks.
Why Small Businesses?

71% is a huge number. This mammoth amount of attacks on these businesses is not out of the blue. There are reasons and causes that lead to this situation.
One thing is obvious, these businesses are not really paying attention to their online assets. Websites, servers, and apps are not protected. At least not protected as they should be. Find below a few reasons that justify these attacks.
1. Lack of Self-Belief
A lot of the small companies don’t take themselves seriously. In the sense that they don’t believe that they are important enough for a cyber-attack.
They are of the view that the data or monetary value that they hold is not big enough to get that kind of attention. Well, that’s not entirely true. The aim behind a cyber- attack vary. They range from simply proving a point to make a statement.
Getting into a database to taking down a website that can help a direct competitor. This does not mean that a competitor orchestrated an attack. There can be so many reasons for an attack and not all will make sense.
2. Money Matters
Les not kid around and evaluate what it really boils down to. Money! No matter how vigilant one is, there’s hardly any good protection that does not cost a decent amount.
This lack of money forces companies to neglect their cyber security. This willingness to take actions are limited by this resource. No worries there are cybersecurity solutions which will not take up a lot of money and give you decent cover. Read on!
3. Skills
For those that realize their self-worth and have sufficient funds aren’t guaranteed safety. Money is important but not everything. Networks, websites, and apps all need working at the back end conducted by humans. This is where vulnerability may lie. No matter how much is invested and precautions are taken an unaware workforce will always be a potential loose end.
This ever-evolving world demands change. Not only for good but from those who want to excel in sinister plans as well.
Cyber-attacks also undergo evolution and new techniques and vulnerabilities surface every now and then. Training and updating employees with the latest trends and safe practices can be a highly effective way to secure small businesses from a cyber-attack.
Cyber-attacks

To counter a threat requires knowledge of one. Knowing a threat is a way that equips you to understand and take measures to deal with one. We’ve lined up a few common types of cyber-attacks. Check them out and stay secure!
1. Password attack
A password is the most common technique used as a security measure. It is a key to the locker which has our precious belongings. The possessing it has the access to whatever is hidden. Similarly, password protection requires a password to access files, documents, etc. The same password is the wrong hand is a disaster.
Interestingly getting a password is not just making wild guesses. Sneaking around the desk or ‘sniffing’ can easily give away the real password without much effort. Leaked password leads to open networks and access to those areas where only authorized personnel are allowed.
2. Malware attack
Let’s first know what a malware is. It is an unwanted software in a device that sits back and spies on you. It can be introduced by inserting a storage device into a system, email or plainly via the internet. Malware has the ability to regenerate and multiply. They can also spread from one device to another via the internet. Read on to know some of the common malware:
- Macro viruses
- File infectors
- System or boot-record infectors
- Polymorphic viruses
- Trojans
- Logic bombs
- Worms
3. MitM attack
MitM or man-in-the-middle attack is what the term suggests. What actually happens is that an attacker jumps in between the server and a legitimate device. This enables the attacker to monitor and control the connection. The three types of MitM attacks are:
- Session Hijacking
- IP Spoofing
- Replay
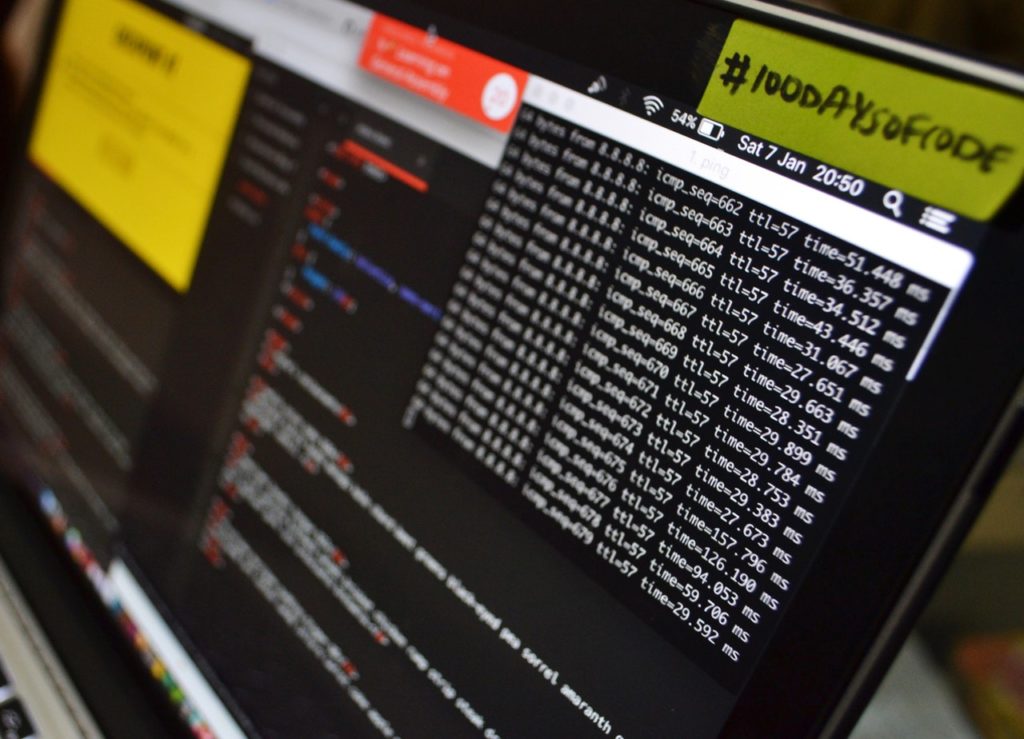
4. DDoS attack
A DDoS or denial-of-service attack is about overloading a system with requests. An overwhelming number of requests are sent to a server. These requests slowly start to pile up which results in no response to requests. Such an attack is carried out by legitimate but hacked devices.
There are multiple kinds of DDoS attacks. The notorious ones are TCP, SYN flood attack. Knowing a threat is one thing and countering is another. Based on what kind of threat you are looking for enables you to ward off any potential threats. Your strategy to fight a DDoS attack can be dealt in many ways. Know the threat and choose a strategy to stay secure.
Read Also: Boost Your Internet Security with These 5 Easy-to-Implement Tips
Build a strong shield with 3 Cybersecurity Solutions
There is a scientific way to go about solving a problem. The first step in this process is to know what the problem is. Knowing the problem leads to the importance of its solution. We know what the problem is. A little light on the common types further elaborates the trouble at hand. It is time to dig right into possible cybersecurity solutions.
1. Strengthen those passwords
Let’s not get into the basics of a password. We all know it works. Password attacks are the most common type of attacks. Why? Simply because the password is the most common type of security protocol used. The most common used lock is the most broken in to. Coming up with a great password is simple yet effective. A little effort goes a long way.
Password attacks are the ones that usually cause data breaches. The passwords were either lost, stolen or simply simple enough to be easily guessed. Losing a password sounds silly, but then again so does a wallet, a phone or earphones. A password is a combination of characters on a keyboard. The variation is great which makes it hard to guess. This is exactly why stealing a password is easier than guessing one.
Stealing a password save over a CD? Must take an Ethan Hunt to steal one. Nope, it is much simpler. People write a password on a piece of paper and place it on the table. They either forget it there, throw it in a wastepaper basket or it simply gets stolen.
A more interesting way to obtain passwords is through a rogue device. This device is connected to a network or a device such as a printer. This enables a malware to enter the network without being noticed. Once the malware is through it then sits back spies and shares the data. In this case passwords. This reminds me of a movie, “Troy”. An attack out of nowhere.
Safe password practices are necessary. Have your employees change their passwords every 60-90 days. This is how often the change in passwords need to be. To ensure further safety, have them form a strong password. Uppercase letters, lowercase letters, number, and symbols. They add up to form an almost herculean password.
2. Secure Connection
Wi-Fi can be an easy way to access the network. Once connected, we all know what can be done once inside the network. This treat can be managed. That too without spending a lot. The easiest way to go about will be to set up a different Wi-Fi for clients. Limited password share among the employees is another way to manage the threat. This results in limited network access which results in lower threat levels.
Getting protective software is another solution. Deal with the attack before the castle is breached. Getting an internet connection that comes with such software is a simple method. You can also choose from a variety of other options. Get one on your own and feel safer and relax.
3. Train you’re your army
Here’s the thing with humans, we are all unique. Everyone is not the same and not everyone has the same knowledge. Some will be good at one thing while the others will be proficient in something different. Similarly, not everyone is tech savvy. Especially when it comes to the knowledge of hacking and cyber-attacks. Such members of your team will need education on this which will need to be followed up with focused training.
Here’s something for those who know it all. We have previously established that the technology is constantly evolving. The ones that claim to know everything may have missed something new. They are not professionals in the field. These people will need refreshers and update training. This will keep them sharp and you safe!
Wrap up!
Securing networks, websites and apps is a difficult task. The process is lengthy and expensive. The complexity and expense do not ensure complete 100% security. Even Facebook faces data breaches. The lesson to pick here is that do the best you can with the resources at your disposal. You and your business are important. Stay safe, Stay online!
Read Also:
- 4 Reasons Why You Need Cyber Insurance
- 4 Security Issues Every Small Business Needs to Prepare For
- 5 Big Technology Brands that Are Watching You in Your Privacy
- 7 Business Data Management Tools That Can help You Grow
Author Bio: Nathan John works as a content editor at Cox internet packages. He has seven years of experience in content writing and he contributes on various online communities.